Twitter has been dying since 2009, and commentators have pre-emptively declared it deceased pretty much every year since. To declare that it’s on the downturn has become a bit of a cliché. But that doesn’t mean that it isn’t also, well, true.
Grumbling among users and commentators has grown to a roar over the past few days, thanks in part to a Buzzfeed report (refuted by Jack Dorsey, Twitter’s CEO) claiming the service will move away from a chronological timeline and towards an algorithmic one. Users coined the hashtag #RIPTwitter in response, and, tellingly, many of their complaints spanned beyond the apparently erroneous report.
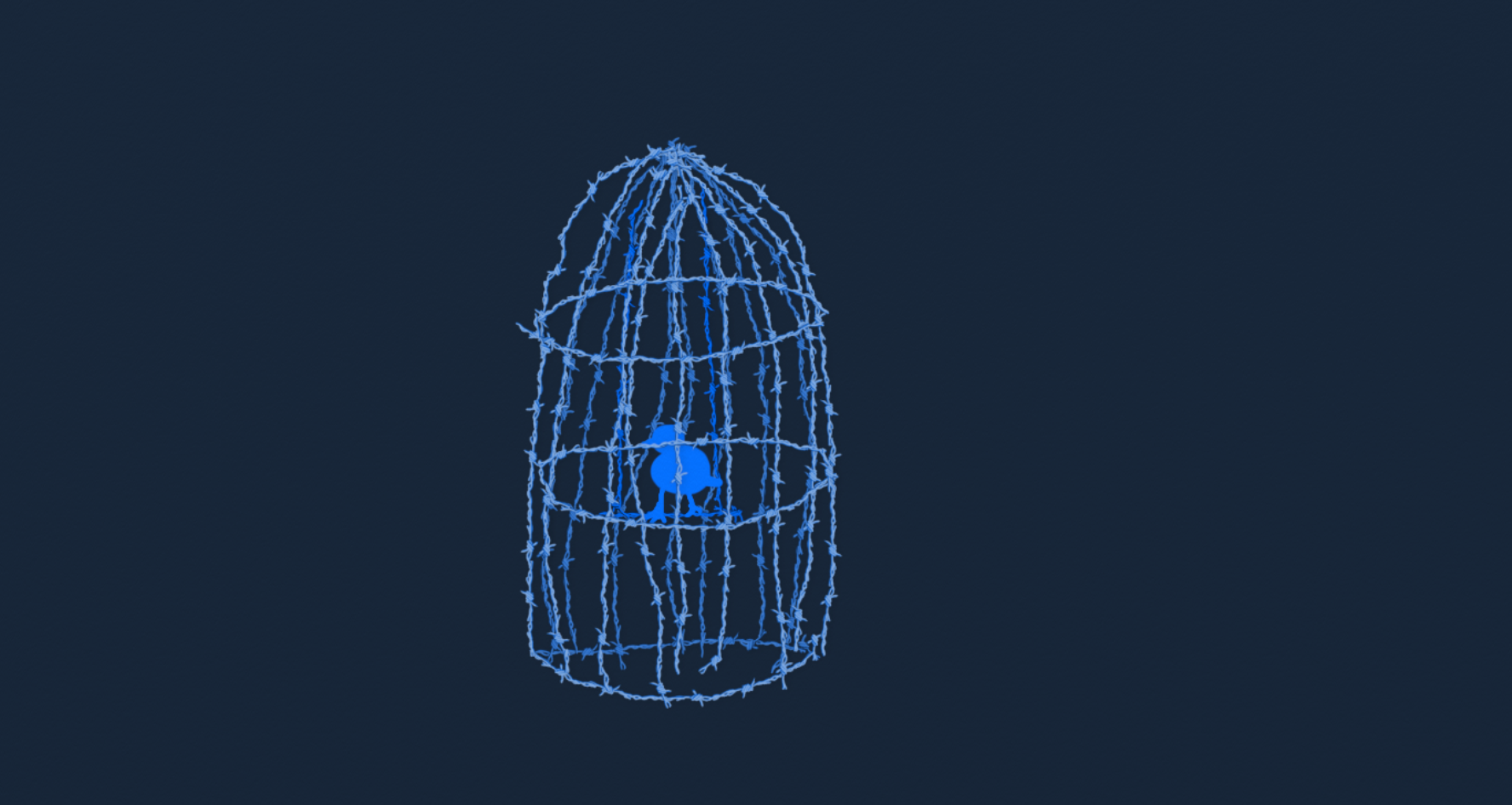
They join a clutch of other murmurings, bits of data and suggestions that things are not as they should be in the Twitter aviary.
Below is one response to the threat of the new timeline, aptly showing that for lots of users, the new feed would have been the straw that broke the tweeters’ backs:
us: twitter we want an edit button
twitter: 10k limit?
us: no we want an edit bu-
twitter: ok algorithmic timeline i got u fam#RIPTwitter— JYLAH TRASH #1 (@twinklrhowell) February 6, 2016
Twitter first announced it was considering a new 10,000 character limit in January, but it’s yet to be introduced. Reactions so far indicate that no one thinks this is a good idea, as the 140 character limit is so central to Twitter’s unique appeal. Other, smaller tweaks – like an edit button – would probably sit much more easily within Twitter’s current stable of features, and actually improve user experience:
.@jack stop messing with it. It’s a 140 characters. It’s not that bloody difficult. Concentrate on the edges: editing, abuse, search.
— Samer Farha (@samerfarha) February 6, 2016
While Dorsey completely denied that the change would take place, he then followed up with an ominous suggestion that something would be changing:
I *love* real-time. We love the live stream. It’s us. And we’re going to continue to refine it to make Twitter feel more, not less, live!
— Jack (@jack) February 6, 2016
“It’ll be more real-time than a feed playing out in real time!” probably isn’t going to placate users who think the existing feed works just fine. It may be hard to make youself heard on the current timeline, but any kind of wizardry that’s going to decide what’s “timely” or “live” for you is surely going to discriminate against already alienated users.
I’ve written before about the common complaint that Twitter is lonely for those with smaller networks. Take this man, who predicts that he’ll be even more invisible in Twitter’s maelstrom if an algorithm deems him irrelevant:
Twitter for me is the difference between being alone and being lonely. With algorithms I’ll potentially be invisible again. #RIPTwitter
— Warren Loves Pips (@dunhilllloyd) February 6, 2016
What’s particularly troubling about Twitter’s recent actions is the growing sense that it doesn’t “get” its users. This was all but confirmed by a recent string of tweets from Brandon Carpenter, a Twitter employee who tweeted this in response to speculation about new features:
Seriously people. We aren’t idiots. Quit speculating about how we’re going to “ruin Twitter”
— Brandon Carpenter (@bhcarpenter) February 6, 2016
…and then was surprised and shocked when he received abuse from other accounts:
Wow people on Twitter are mean
— Brandon Carpenter (@bhcarpenter) February 6, 2016
This is particularly ironic because Twitter’s approach (or non-approach) to troll accounts and online abusers has made it a target for protest and satire (though last year it did begin to tackle the problem). @TrustySupport, a spoof account, earned hundreds of retweets by mocking Twitter’s response to abuse:
Today we’re excited to announce a faster way to report abuse.
1. Download this image
2. Email it to yourself pic.twitter.com/SZMGMnd112— Trusty Support (@TrustySupport) February 2, 2016
Meanwhile, users like Milo Yiannopolous, who regularly incites his followers to abuse and troll individuals (often women and trans people, and most famously as part of G*merg*te), has thrived on Twitter’s model and currently enjoys the attentions of almost 160,000 followers. He has boasted about the fact that Twitter could monetise his account to pull itself out of its current financial trough:
.@nero on Breitbart News Daily: Twitter ‘could be making a fortune’ if it properly monetized my account https://t.co/vckPWh6jdn
— Breitbart News (@BreitbartNews) January 12, 2016
The proof of any social media empire’s decline, though, is in its number and activity of users. Earlier this month, Business Insider reported that, based on a sample of tweets, tweets per user had fallen by almost 50 per cent since last August. Here’s the reporter’s tweet about it:
Leaked Twitter API data shows the number of tweets is in serious decline https://t.co/shKbut4H7j pic.twitter.com/fFsJwtCwt9
— Jim Edwards (@Jim_Edwards) February 2, 2016
Interestingly, numbers of new users remained roughly the same – which implies not that Twitter can’t get new customers, but that it can’t keep its current ones engaged and tweeting.
Most tellingly of all, Twitter has stopped reporting these kinds of numbers publicly, which is why Jim Edwards had to rely on data taken from an API. Another publication followed up Edwards’ story with reports that users aren’t on the platform enough to generate ad revenue:
For those of u who didn’t believe my story https://t.co/shKbut4H7j yesterday about Twitter, The Information says: pic.twitter.com/eT5CLDf6XG
— Jim Edwards (@Jim_Edwards) February 3, 2016
The missing piece of the puzzle, and perhaps the one thing keeping Twitter alive, is that its replacement hasn’t (yet) surfaced. Commentators obsessed with its declining fortunes still take to Twitter to discuss them, or to share their articles claiming the platform is already dead. It’s ironic that the most heated discussions of the platform’s weaknesses are playing out on the platform itself.
For all its faults, and for all they might multiply, Twitter’s one advantage is that there’s currently no other totally open platform where people can throw their thoughts around in plain, public view. Its greatest threat yet will come not from a new, dodgy feature, but from a new platform – one that can actually compete with it.





