
The “like” button is perhaps the simplest of the website’s features, but it’s also come to define it. Companies vie for your thumbs up. Articles online contain little blue portals which send your likes back to Facebook. The action of “liking” something is seen to have such power that in 2010, a class action lawsuit was filed against Facebook claiming teenagers should not be able to “like” ads without parental consent.
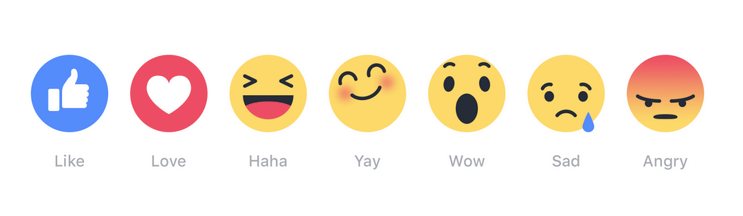
And today, Facebook begins trials of six new emoji reaction buttons which join the like button at the bottom of posts, multiplying its potential meanings by seven:
All this makes it a little surprising that Facebook CEO Mark Zuckerberg spent a good portion of the noughties giving the like button a thumbs down. According to Andrew Bosworth, Vice President of Advertising and Pages at Facebook (and known simply as “Boz”) it took nearly two years to get the concept of an approval button for posts off the ground.
In a fascinating Quora thread, Boz explains that the idea of a star, plus sign or thumbs up for posts first came up in July 2007, three years after “TheFacebook” launched in 2004. Throughout these initial discussions, the proposed bursts of positivity was referred to as an “awesome button”. A few months later someone floated the word “like” as a replacement, but, according to Boz, it received a “lukewarm” reception.
The team who ran the site’s News Feed feature were keen, as it would help rank posts based on popularity. The ad team, meanwhile, thought “likes” could improve clickthrough rates on advertisements. But in November 2007, the engineering team presented the new feature to Mark Zuckerberg, and, according to Boz, the final review “[didn’t] go well”. The CEO was concerned about overshadowing the Facebook “share” and comment features – perhaps people would just “awesome” something, rather than re-posting the content or writing a message. He also wanted more clarification on whether others would see your feedback or not. After this meeting, Boz writes, “Feature development as originally envisioned basically stops”.
The teams who wanted the button forged ahead with slightly different features. If you were an early user, you might remember that News Feed items and ads collected positive or negative feedback from you, but this wasn’t then displayed to other users. This feature was “ineffective”, Boz writes, and was eventually shut down.
So when Jonathan Piles, Jaren Morgenstern and designer Soleio took on the like button again in December 2008, many were skeptical: this was a “cursed project”, and would never make it past a sceptical Zuckerberg. Their secret weapon, however was data scientist Itamar Rosenn, who provided data to show that a like button wouldn’t reduce the number of comments on a post. – that, in fact, it increased the number of comments, as likes would boost a popular post up through the News Feed. Zuckerberg’s fears that a lower-impact feedback style would discourage higher value interactions like reposting or commenting were shown to be unfounded.
A bigger problem was that FriendFeed, a social aggregator site which shut down in April 2015, launched a “like” feature in October 2007, a fact which yielded some uncomfortable media coverage when Facebook’s “like” finally launched. Yet Boz claims that no one at Facebook clocked onto FriendFeed’s new feature: “As far as I can tell from my email archives, nobody at FB noticed. =/”.
Finally, on 9 February 2009, “like” launched with a blogpost, “I like this“, from project manager Leah Pearlman who was there for the first “awesome button” discussions back in 2007. Her description of the button’s purpose is a little curious, because it frames the feature as a kind of review:
This is similar to how you might rate a restaurant on a reviews site. If you go to the restaurant and have a great time, you may want to rate it 5 stars. But if you had a particularly delicious dish there and want to rave about it, you can write a review detailing what you liked about the restaurant. We think of the new “Like” feature to be the stars, and the comments to be the review.
Yet as we all know, there’s no room for negative reviews on Facebook – there is no dislike button, and there likely never will be. Even in the preliminary announcements about the new emoji reactions feature, Zuckerberg has repeatedly made clear that “dislike” is not a Facebook-worthy emotion: “We didn’t want to just build a Dislike button because we don’t want to turn Facebook into a forum where people are voting up or down on people’s posts. That doesn’t seem like the kind of community we want to create.”
Thanks to the new buttons, you can be angry, excited, or in love with other people’s content, but the one thing you can’t do is disapprove of its existence. Championing positivity is all well and good, but Zuckerberg’s love of the “like” has more to do with his users’ psychology than it does a desire to make the world a happier place. Negative feedback drives users away, and thumbs-down discourages posting. A “dislike” button could slow the never-ending stream of News Feed content down to a trickle – and that, after all, is Facebook’s worst nightmare.





